Today, online data protection has become a priority for both individual users and organizations. Many turn to solutions like virtual private networks (VPNs), believing they guarantee complete anonymity. But to what extent is this true? Is a VPN enough to protect our most sensitive data?
In this article, we analyze the key differences between VPNs and anonymization techniques, two tools that are often confused but serve different needs. We’ll explore what they actually protect, how they do it, in what scenarios they are useful, and, most importantly, why relying solely on a VPN could be a mistake when it comes to regulatory compliance and online data protection. If you work with personal or sensitive data, such as in sectors like healthcare, banking, or legal, this analysis can help you understand why anonymization techniques are an indispensable solution today.
What is a VPN and how does it work?
A VPN (Virtual Private Network) is a technology that establishes a secure, encrypted connection between your device and the internet. When using a VPN, all your data traffic is redirected through a remote server operated by the service provider, hiding your real IP address and encrypting the information you send and receive. This makes it difficult for third parties, such as Internet Service Providers (ISPs), hackers, or government agencies, to track your online activities or intercept your data.

Why is it considered a secure method?
VPNs offer several layers of protection that make them a popular tool for improving online data protection:
- Data encryption: They use advanced security protocols to encrypt information, protecting it from unauthorized access.
- IP cloaking: When connecting through a VPN server, your real IP address is replaced with that of the server, making it difficult for your location and online activities to be tracked.
- Secure remote access: They allow employees and users to securely access corporate networks from remote locations, protecting sensitive information.
These features make VPNs especially useful when connecting to public Wi-Fi networks, where security risks are higher, which explains their growing use not only at the business level but also at the personal level.
How widely used are VPNs?
VPN use has grown significantly in recent years, establishing itself as one of the most popular tools for strengthening online data protection. In 2024, an estimated 1.6 billion people worldwide will use VPNs, equivalent to 31% of internet users. This trend reflects a growing concern about digital security and has boosted the global VPN market, valued at $50.9 billion in 2023 and projected to reach $137.7 billion by 2030, with an annual growth rate of 15.3%. Furthermore, a survey conducted by TechRadar in May 2025 showed that 73% of respondents regularly use a VPN, and 79% do so specifically to improve their online privacy.
According to data from Forbes Advisor, more than 67% of VPN users use them to maintain their anonymity online, while 50% do so to secure their data on public networks, and 30% seek to circumvent censorship or access geo-blocked content. This reinforces the perception of VPNs as allies of digital privacy, although their actual capabilities don’t always meet expectations in all contexts.
As can be seen, these data reflect a growing awareness of the importance of online data protection, driving the adoption of VPNs as a secure method. However, this widespread trust doesn’t always translate into complete protection, especially when it’s unknown what data the provider collects or when it’s not combined with other measures such as anonymization.
What are anonymization techniques?
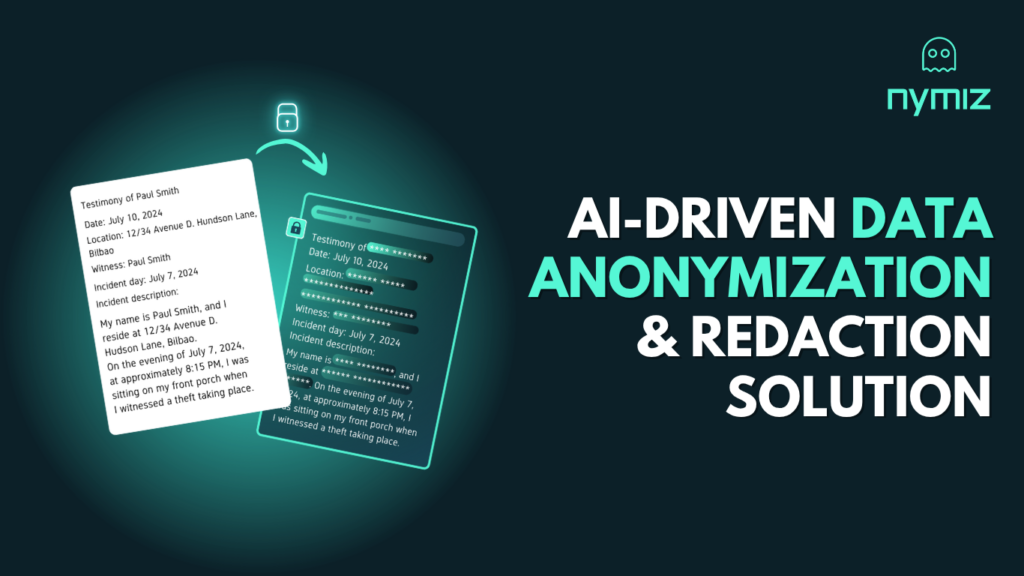
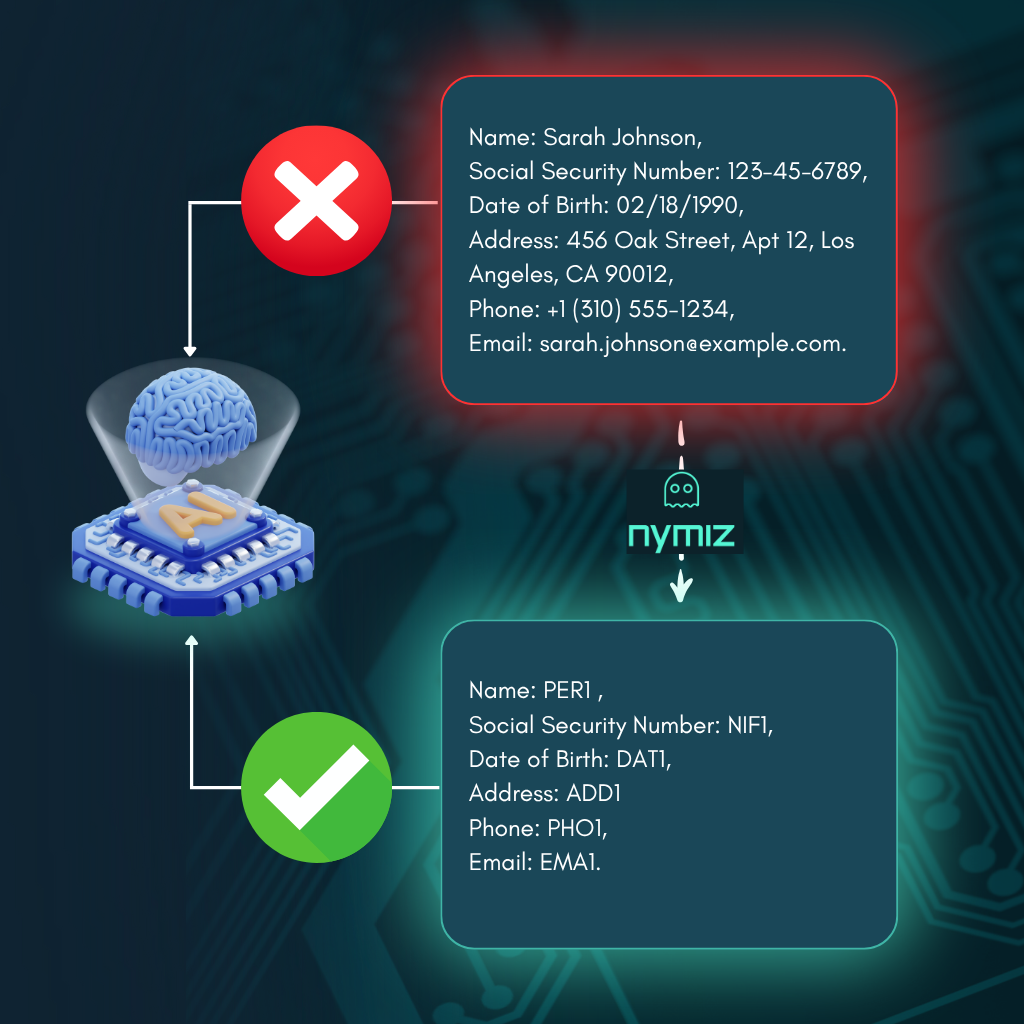
Anonymization techniques are methods applied to the processing of personal data to prevent a person from being directly or indirectly identified. Unlike a VPN, which protects data in transit, anonymization acts on the content of the data, transforming it in such a way that the identity of the data subject cannot be deduced, even if the data were exposed.
Its main purpose is to protect privacy, especially in contexts such as healthcare, research, or the legal sector, where large volumes of sensitive information are handled. These techniques allow data to be analyzed and shared without jeopardizing the identity of the individuals involved, making them an essential tool in the era of big data and artificial intelligence.
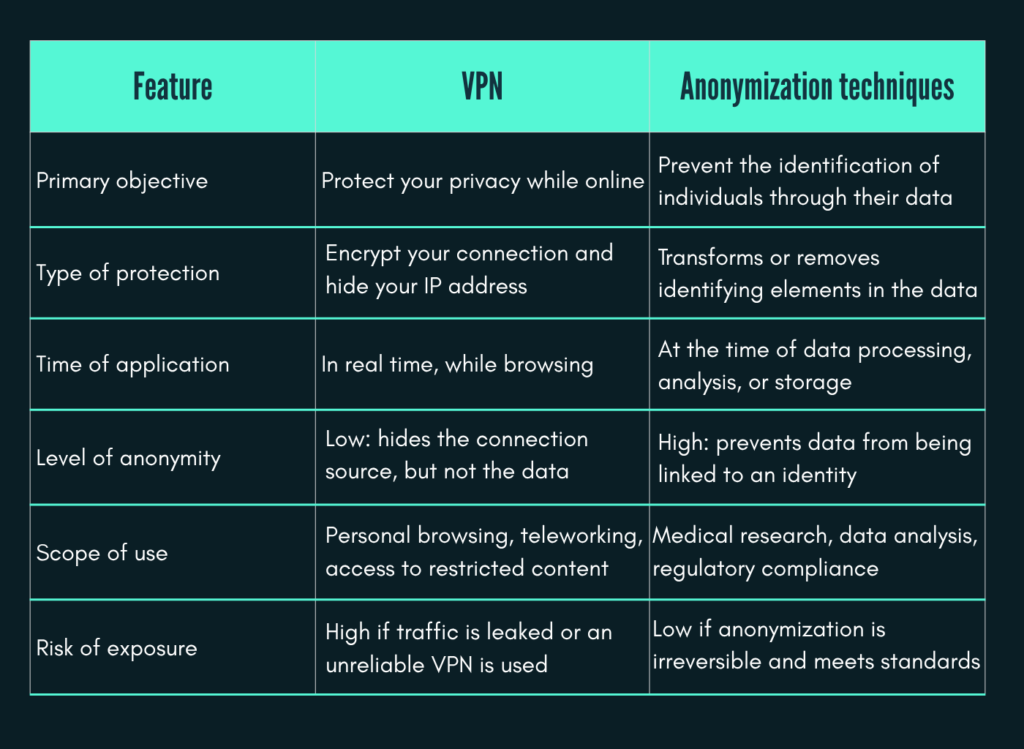
How do they differ from a VPN?
Although VPNs and anonymization techniques are often grouped under the umbrella of data protection, their differences are fundamental in both purpose and scope. Understanding them is key to choosing the right tool for the context. Below is a table to differentiate each technique according to its objective, type of protection, scope of use, and risk level:
Common anonymization methods
Below, we explain the most commonly used techniques for anonymizing sensitive data without exposing the identity of the individuals behind the information:
- Anonymization: The irreversible removal or transformation of all elements that could identify a person. This is the most secure method, as it prevents re-identification even with additional data.
- Pseudonymization: The replacement of real identifiers with pseudonyms. Although it reduces the risk of identification, data can be re-identified if a matching system is in place.
- Tokenization: The replacement of sensitive data with alternative values (tokens) with no intrinsic meaning. It is particularly used in financial and healthcare settings to preserve the structure without exposing the content.
- Synthetic Data: The generation of completely fictitious data that is statistically equivalent to real data. It is useful for training AI models without using real data about people.
These techniques are key pillars of regulatory compliance (such as the GDPR or the AI Act) and the responsible development of technologies such as artificial intelligence and machine learning.
When to use a VPN and when to anonymize data
Below, we explore specific situations that show when it’s best to use a VPN and when it’s better to opt for anonymization techniques.
Recommended use cases for VPNs:
- Secure browsing on public or insecure networks.
- Hiding your location or bypassing geo-restrictions.
- Protecting connection data in remote work environments.
Recommended use cases for anonymization techniques:
- Sharing sensitive data with third parties (for example, in biomedical research).
- Complying with regulations such as the GDPR when processing personal data.
- Training artificial intelligence models without using identifiable information.
In short, a VPN protects how and from where you connect, while anonymization protects what data you share or analyze. Far from being mutually exclusive technologies, the two can be complementary depending on the privacy and security needs of each scenario.
Why isn’t a VPN enough to protect your data?
Although VPNs (Virtual Private Networks) are widely used tools to enhance online data protection, their protection is limited and should not be confused with advanced anonymization methods. Their primary function is to encrypt the internet connection and hide the IP address, thereby protecting data in transit. However, this layer of security doesn’t cover multiple vectors of personal data exposure.
1. VPNs don’t prevent tracking through cookies or fingerprinting techniques. Websites can still identify users through unique browser fingerprints, operating system, or device settings, regardless of the IP address they are using.
2. A VPN doesn’t anonymize stored data. Any personal information provided to a service (such as name, address, or browsing habits) is still exposed if complementary techniques such as anonymization or tokenization are not applied.
3. Another major limitation is the lock-in to the VPN provider. Even if they promise not to keep logs, some free or poorly managed services have been flagged for recording or even selling browsing data. There are also technical vulnerabilities such as DNS or WebRTC leaks, which can reveal the user’s real IP address even with the VPN active.
4. A VPN doesn’t protect against local threats, such as malware already present on the device, nor does it guarantee the security of apps or platforms that use data. In fact, 57% of users have experienced some type of cyberattack while using a VPN, demonstrating that these tools don’t offer complete coverage when it comes to online data protection, especially if not accompanied by other strategies such as anonymization.
For these reasons, VPNs are a useful tool but insufficient on their own to guarantee comprehensive privacy protection. In contexts where compliance with regulations such as the GDPR is required, or where sensitive data is handled, it is essential to adopt complementary strategies such as advanced anonymization, pseudonymization, or synthetic data generation.
The dark side of VPNs: Real privacy risks of trusting the wrong provider
Although VPNs encrypt the connection and hide the IP address, traffic passes through the provider’s servers. If the provider doesn’t have clear privacy policies, keeps logs, or collaborates with third parties, data can be leaked or sold.
Furthermore, VPNs don’t apply anonymization. That is, they don’t eliminate the possibility of data being traced or linked to an individual. Techniques such as tokenization or the use of synthetic data are necessary to ensure regulatory compliance and privacy.
Real-life cases:
- In 2022, more than 21 million users were affected by a breach involving three free VPNs (SuperVPN, GeckoVPN, and ChatVPN). Emails, passwords, and IP addresses were exposed.
- Some services declared as “no logs” have been court-ordered to hand over logs, revealing that they stored more information than they claimed.

Using a VPN without knowing the provider can be more dangerous than not using one at all. True privacy requires combining encryption with anonymization and additional security controls.
Regulatory compliance: What does the law say about VPN use?
Virtual private networks (VPNs) are legal tools in Spain and most countries around the world. Their use is permitted as long as they are used ethically and not for illegal activities, such as downloading illegal content or unauthorized access to systems.
Legality of VPN use in Spain and the European Union
In the Spanish and European context, VPNs are considered legitimate tools for protecting online data protection. There are no specific legal restrictions prohibiting their use. However, it is essential to use them responsibly and in compliance with the law.
The GDPR and personal data protection
The General Data Protection Regulation (GDPR) establishes a legal framework for the protection of personal data in the European Union. Although the GDPR does not explicitly mention VPNs, it does impose obligations on organizations regarding the security of data processing. This includes implementing appropriate technical and organizational measures to ensure a level of security appropriate to the risk.
Therefore, the use of VPNs can be part of a broader security strategy to protect personal data, but it does not exempt organizations from complying with all GDPR obligations.
Legitimate use cases and regulatory risks
Legitimate use cases for VPNs include:
- Protecting privacy on public networks.
- Secure access to corporate networks.
- Bypassing censorship in countries with content restrictions.
However, using VPNs for illegal activities, such as circumventing geo-restrictions to access copyrighted content or engaging in criminal activity, may have legal consequences.
Legality and restrictions in other countries
Although VPNs are legal in most countries, there are exceptions where their use is restricted or prohibited:
- China: Only government-approved VPNs are allowed.
- Russia: Significant restrictions and blocking of VPN services.
- Iran: Use restricted and monitored by the government.
- North Korea: Complete ban on VPN use.
It’s essential to keep this list to verify the legality of VPN use, both in your country of residence and in those you travel to. Not only will you avoid potential legal consequences, but you’ll also be actively strengthening the protection of your online data.
When should you use a VPN and when should you use anonymization techniques?
The choice between a VPN and anonymization techniques depends on the data protection objective and the context in which they are used. Below are practical recommendations and real-world examples by industry:
Healthcare Sector
VPN: To allow medical personnel to securely access hospital systems from remote locations, protecting information during transmission.
Anonymization: When sharing patient data for research, anonymization techniques are applied to remove personal identifiers, ensuring privacy and regulatory compliance.
Legal Sector
VPN: Allows lawyers and legal staff to securely access confidential documents and communications from outside the office, protecting information in transit.
Anonymization: When publishing rulings or legal documents, anonymization techniques are used to protect the identity of the parties involved, complying with data protection regulations.
Technology and Business Sector
VPN: Allows remote employees to securely access corporate networks, protecting sensitive information while connected.
Anonymization: When analyzing large volumes of user data, anonymization techniques are applied to extract insights without compromising individual privacy, complying with regulations such as the GDPR.
VPNs are ideal for protecting information during transmission, especially over remote connections, while anonymization techniques are essential for protecting privacy when sharing or analyzing stored data. The combination of both strategies provides comprehensive data protection in a variety of contexts.
Conclusion: Beyond a VPN, toward real data protection
VPNs have gained popularity as digital protection tools. However, their exclusive use can create a false sense of security. Although they protect the connection and hide the IP address, they do not prevent data collection by third parties, nor do they guarantee the privacy of stored or shared information.
In a context where personal data is the new digital gold, relying solely on a VPN is like locking the front door and leaving the windows open. Real protection requires a more comprehensive strategy, encompassing everything from encryption in transit to effective anonymization of sensitive data, especially when it is stored, shared, or processed for analytics and artificial intelligence.
Online data protection cannot rely on a single tool. It must be supported by an ethical, technological, and regulatory approach that is tailored to the type of information we manage and the real risks of the digital environment.
Ready to go a step further?
Discover how to intelligently anonymize your data with Nymiz and lead a digital transformation that respects online data privacy and ensures regulatory compliance.
Book your personalized demo and start truly protecting your information.